2022 saw cases continue to be filed under the California Consumer Privacy Act (“CCPA”), although perhaps reflecting the increasing reliance of the plaintiffs’ bar on negligence and tort-based privacy claims concerning a defendant’s alleged failure to maintain “reasonable security,” the number of cases of CCPA based claims declined. Read on for Privacy World’s highlights of the year’s most significant events concerning the CCPA, as well as our predictions for what 2023 may bring.
Background
The CCPA went into effect on January 1, 2020, with the vast majority of its provisions applying to entities that qualify as “businesses.”
As a recap, what entities qualify as a business under the CCPA? The statute defines a business as a for-profit, private entity that (1) collects “personal information”, (2) determines the purposes and means of processing that personal information, (3) does business in California, and (4) meets certain revenue thresholds (>$25 million global gross revenue annually) and/or data collection/selling/sharing thresholds.
In addition to imposing numerous compliance obligations* on businesses, CCPA covered businesses are also subject to the law’s limited private right of action for certain security breaches.
*While the majority of this post focuses on the private right of action and enforcement-related issues, for those interested in the CCPA’s compliance obligations, effectiveness of the California Privacy Rights Act (“CPRA,”* which substantially amends the CCPA and became effective as of Jan. 1 this year), applicability of the CCPA to human resources and business-to-business data, and information on other state privacy laws, please see our recent post Are You Ready for the 2023 Privacy Laws? *References to CPRA in the remainder of this article mean the CCPA as amended by the CPRA, unless otherwise indicated.
Back to the private right of action, Section 1798.150(a)(1) of the CCPA provides a private right of action to “[a]ny consumer whose nonencrypted and nonredacted personal information … is subject to an unauthorized access and exfiltration, theft, or disclosure” due to a business failing to satisfy “the duty to implement and maintain reasonable security procedures and practices….” (emphasis supplied).
Damages available for a private right of action under Section 1798.150(a)(1) include a statutory amount of between $100 and $750 “per consumer per incident or actual damages, whichever is greater”, as well as injunctive or declaratory relief and “any other relief the court deems proper” (emphasis supplied).
CCPA Litigation Activity in 2022
Since the CCPA came into effect, nearly 300 cases have been filed by plaintiffs alleging violations of the statute. The majority of these have been filed in California federal court (Northern and Central Districts of California being the most favored jurisdiction for such filings), with some also being brought in California state court and in other jurisdictions.
Although the number of CCPA filings declined from 2021, this may be due to the plaintiffs’ bar shifting towards alleging negligence and tort-based privacy claims in the wake of a data event. This can be explained in part that such claims typically (although not always) are less burdensome to plead for them to survive past the motion to dismiss stage. By contrast, it appears that based on at least rulings thus far courts have attempted to narrowly construe the CCPA’s limited private right of action.
Courts have consistently dismissed CCPA claims when it is clear from the face of the complaint that Plaintiff’s allegations do not concern a security breach as required to plead a civil cause of action under the CCPA. Additional rulings this year reinforced the temporal requirements of the statute (that it must involve conduct arising as of the CCPA’s date of enactment, not before) and that the CCPA could not be relied upon by a defendant as a basis for refusing to comply with its discovery obligations in litigation. Although many CCPA litigations involve software based claims and the tech industry in the wake of a data breach, healthcare and financial services entities, among others, have also been targeted.
CCPA Claims, Article III standing and Settlement Activity
As longtime readers of the blog are aware, Article III standing in the context of data privacy cases is in a constant state of flux—particularly in the Ninth Circuit.
When a CCPA claim is asserted in federal court, it must meet that “irreducible minimum,” as it is frequently described. Article III standing consists of 1) suffering some actual or threatened injury; 2) fairly traceable to the defendant; which 3) is likely to be redressed by a favorable decision. The injury must be concrete, rather than abstract, and particularized, meaning that it affects the plaintiff in a personal and individual way. Spokeo, Inc. v. Robins, 578 U.S. 330, 339 (2016). But as the Supreme Court held in 2021, “an injury in law is not an injury in fact,” and a plaintiff must do more than show a bare statutory violation for a claim to exist. TransUnion LLC v. Ramirez, 141 S. Ct. 2190, 2205 (2021).
In Kirsten, 2022 WL 16894503, the Central District of California addressed a defendant’s contention that a plaintiff lacked standing to pursue a CCPA claim, among others, because they could not fairly trace instances of identity theft, fraudulent credit card charges, and inability to access online accounts to the data breach at issue. The court rejected the defendant’s argument, holding instead that past injury from misappropriated personal information gave rise to a substantial risk of threatened injury in the future. Particularly notable is the court’s premising standing both on the actual injuries the plaintiffs experienced and the injuries they might experience in the future.
In Hayden v. Retail Equation, Inc., 2022 WL 2254461 (reconsidered and vacated in part on other grounds), the Central District of California addressed the specific requirements necessary to give rise to an injury under the CCPA. Plaintiffs, retail consumers, sued a variety of retailers for their use of a “risk scoring” system that collected and shared individualized personal data with a vendor in order to assess the risk of fraud when a consumer attempted a product return or exchange.
Plaintiffs sued under Cal. Civ. Code § 1798.150(a), which required them to show that “nonencrypted and nonredacted personal information” was “subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the business’s violation of the duty to implement and maintain reasonable security procedures and practices appropriate to the nature of the information to protect the personal information.” The Court found that Plaintiffs had not asserted a claim under the CCPA because the disclosure of their information was not the result of a failure to implement and maintain reasonable security procedures and practices; rather, it was “a business decision to combat retail fraud.” Plaintiffs’ failure to allege a violation of specific duties under the CCPA, as opposed to a more generalized complaint about the misuse of their data, could not support their claim. The Hayden court also found that non-California residents lacked standing to bring suit under the CCPA.
The most significant CCPA settlement of 2022 was the $350 million T-Mobile settlement to resolve multidistrict litigation brought by T-Mobile customers whose data was allegedly exposed in a 2021 data breach. In August 2021, T-Mobile disclosed that it had been the victim of a cyberattack that resulted in the compromise of some current, former and prospective customers’ SSN, name, address, date of birth and driver’s license/ID information the “Data Event”). By T-Mobile’s account, no “customer financial information, credit card information, debit or other payment information” was exposed in the attack. Nevertheless, over 40 putative class action claims were filed seeking damages for the improper disclosure of Plaintiffs’ personal information.
On July 22, 2022, Plaintiffs in the T-Mobile case filed an unopposed motion for preliminary approval of a proposed settlement to the class. As part of the settlement, T-Mobile agreed to fund a non-reversionary $350 million settlement fund to pay class claims for out-of-pocket losses or charges incurred as a result of identity theft or fraud, falsified tax returns, or other alleged misuse of a class member’s personal information. The settlement fund will then make payments to class members on a claims-made basis with a $25,000 aggregate claims cap per class member. The proposed settlement also contemplates attorneys’ fees of no more than 30% of the settlement fund, approximately $105 million, and $2,500 individual service awards to class representatives.
2022: Continued Enforcement Activity by California OAG
As we predicted at the end of last year, 2022 saw continued enforcement activity at the state level. Headlines were ablaze in August with California’s Office of the Attorney General announcing its first settlement of a CCPA enforcement action.
Readers of the blog will know that the CA OAG’s CCPA enforcement efforts started in July 2020. While numerous cookie DNS and GPC cases were initially (and quietly) settled by the OAG without monetary penalty or public settlements, that all changed in August 2022 with the OAG announcing its required payment of $1.2 million from a retailer to settle claims of alleged CCPA violations.
The settlement marks a new era of CCPA enforcement in which real repercussions, including monetary penalties, may be imposed. In addition to the settlement, the OAG released “illustrative examples” of other non-public enforcement cases, including the types of violations, remediation activities carried out by the alleged violators, and the alleged violators’ type of business/industry (which included a number of industries that surprised many who thought they were perhaps not on the OAG’s radar for CCPA compliance, such as B2B-focused businesses and companies that are largely (but not fully) exempt from the CCPA, such as healthcare businesses and financial and insurance businesses. For detailed analysis of the OAG’s settlement, see our blog post here.
Litigation and Enforcement in 2023 and Beyond
Litigation
The CPRA’s amendments to the CCPA brought some changes to the private right of action for certain security breaches, namely an expansion of the private right of action where a breach involves data in the form of an email address in combination with a password or security question and an answer that would permit access to an account. In addition, the CPRA’s amendments provide that that remediation of vulnerabilities post-breach are an insufficient cure to preclude statutory damages.
There is not otherwise a private right of action for non-security breach related violations under the CPRA; however, the CPRA opens the possibility of enforcement by all California county district attorneys and the four largest city district attorneys (though that is up for debate). In addition, despite the clarity that the private right of action is limited to certain types of security incidents, it is conceivable that an incomplete or inaccurate response to a consumer request might also give rise to an independent deception claim, and plaintiffs’ lawyers are expected to otherwise test the scope of the limitation on private consumer and class action relief. There is no private right of action for violations of the Virginia Consumer Data Protection Act (“VCDPA”), Colorado Privacy Act (“CPA”), Utah Consumer Privacy Act (“UCPA”), or Connecticut Act Concerning Personal Data Privacy and Online Monitoring (referred to as the “CTPA” herein). Put another way, this means there is not a private right of action for security breaches or security-breach related violations under those laws.
Enforcement
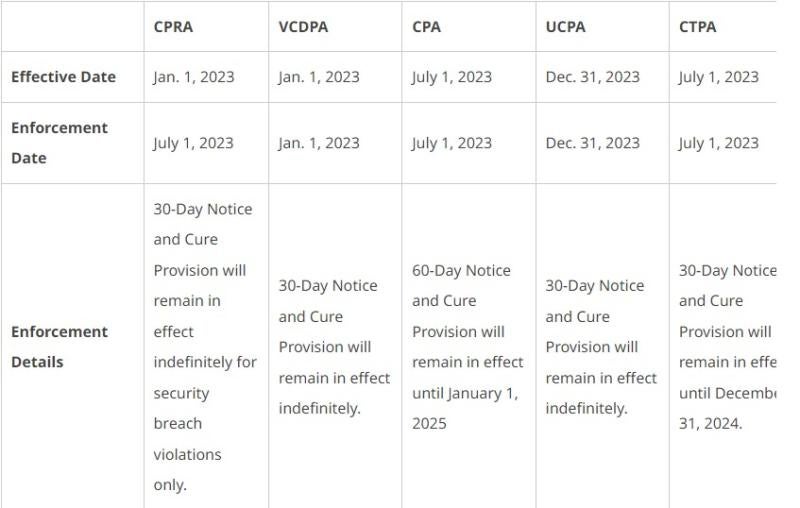
The enforcement risk will certainly increase under the CPRA in 2023 with the California Privacy Protection Agency, or CPPA, enforcing the CPRA alongside the OAG starting on July 1, 2023. In addition to California, Virginia’s privacy law came into effect and was enforceable as of January 1, and privacy laws in Colorado, Connecticut, and Utah will become effective throughout the year (see chart below).
Enforcement of the CPRA is delayed until July 1, 2023 and, unlike the CCPA between its effective and enforcement dates, there is an explicit grace period between January 1 and July 1, 2023. However, the CCPA’s provisions (without the CPRA’s amendments) will remain effective and enforceable between January 1 and July 1, and the required 30-day cure period no longer exists. Importantly, this means that the full scope of the CCPA also currently applies to HR and B2B data, and there is no delay in enforcement with respect to the same.
Under the CPRA, both agencies can seek civil penalties of $2,500 for each violation or $7,500 for each intentional violation or violations involving the data of minors. Violations may be potentially calculated based on each applicable piece of data or consumer, and, thus, exposure could be substantial. The existing requirement in the CCPA to provide notice of violation and give a 30-day cure period before bringing an enforcement action is eliminated by the CPRA, but the law permits the agencies to consider good faith cooperation efforts by the business when calculating the fine, and prosecutorial discretion is not limited. Further, CPPA actions are subject to a probable cause hearing prior to commencement of an administrative enforcement proceeding.
In Virginia, Utah, and Connecticut, the Attorney General has exclusive enforcement authority. The Virginia Attorney General may seek injunctive relief and civil penalties of $7,500 per violation. In Colorado, the state Attorney General or District Attorneys may bring an action for injunctive relief and civil penalties under the Colorado Consumer Protection Act, which provides for civil penalties of $500 per violation, actual damages, or three times actual damages if bad faith is shown. In Utah, the Attorney General may bring an action for actual damages to consumers and civil penalties of up to $7,500 per violation. In Connecticut, the Attorney General may treat a violation of CTPA as an unfair trade practice under the Connecticut Unfair Trade Practices Act (“CUTPA”); however, the private right of action and class action provisions of CUTPA dot not extend to violations of the CTPA. Nevertheless, remedies available for violations of CUTPA include restraining orders; actual and punitive damages, costs, and reasonable attorneys’ fees; and civil penalties of up to $5,000 for willful violations and $25,000 for restraining order violations.
However, like the CCPA (but unlike the CPRA), the respective Attorneys General of Virginia and Utah must provide a controller or processor with 30 days’ written notice of any violation of the VCDPA/UCPA, specifying the provisions that the Attorney General alleges have been violated. In Virginia and Utah, a controller or processor can avoid statutory damages if, within this 30-day cure period, it cures the noticed violation and provides the Attorney General with an express written statement that the alleged violations have been cured and that no further violations will occur. Under Connecticut and Colorado’s laws, their respective AGs must provide violators with notice of alleged violations and an opportunity to cure any such violations within a 60-day period following delivery of the notice. The requirement to allow for a cure period in Colorado sunsets on January 1, 2025 (though, the AG would almost certainly have prosecutorial discretion to allow for a cure). In Connecticut, the cure requirement becomes discretionary on January 1, 2025, as well.
Check back often for our continued updates on privacy litigation and enforcement trends and updates. Privacy World will be there to keep you in the loop.







 />i
/>i

